Is your Visibility Failing you? Where You are getting it Wrong on Cyber Security Visibility
April 23, 2026 • Tom Abuta
Introduction
Imagine an accident happens on your way to work. You're sitting there frustrated, trying to figure out who's at fault. It's even harder for the traffic officer when both drivers refuse to agree on basic traffic rules.
Now imagine one of the vehicles had a dash camera. You watch the video. Suddenly the arguing stops and now you start having a real conversation about how to solve the problem.
Did the dash cam solve the accident? No. But it showed exactly where the problem started. It let everyone go back, see the steps, and pinpoint the real cause.
That idea matters a lot for any organization trying to ensure top cybersecurity posture at all times.
What is Visibility?
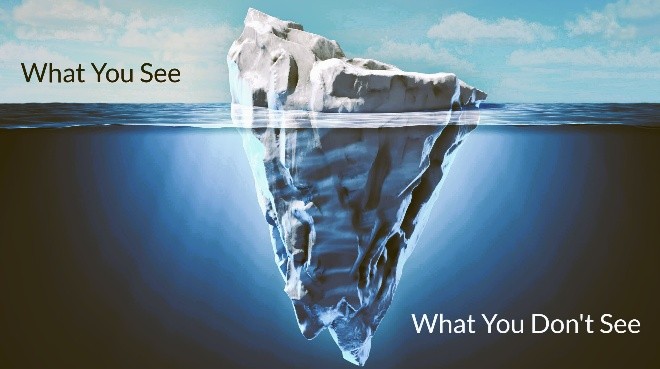
Visibility, simply put, means what you can see at every layer of your system. And it doesn't stop at network logs, endpoint data, or access records. It needs to stretch into the traffic moving through your API infrastructure, and incorporating AI to help make sense of it.
Good cybersecurity visibility helps you understand what assets you actually have and where your real weaknesses are. It doesn't just protect your security—it makes your whole operation run better and faster.
So Where do Organizations Get it Wrong?
1. Focus on Perimeter alone
Too much focus on the perimeter and forget to watch what's happening inside. Some let systems go without updates. Others get buried in security alerts without managing them properly.
This was the case in a Nairobi-based fintech startup. By implementing strong firewalls, they thought their systems were hardened. An attacker was able to compromise through an intern’s laptop and moved laterally for three months. The breach was only discovered by a bank partner, not internally.
2. Access Creep
This is the slow accumulation of unnecessary permissions. user permissions slowly expand over time with no one reviewing them is a security threat. For instance, users who need database access to undertake a project — without proper oversight and revoking of privileges after the project ends — can become a lurking catastrophe.
Recently a temporary IT contractor was given database access for a core banking migration project. After the project ended, his access wasn't revoked. Two years later, that same account (still active) was used in an attempted fraud scheme. Fortunately, early detection stopped it, but the risk had been sitting there for 24 months
3. Data Sitting in unmonitored locations
Widely referred to as shadow data. This is data that is created, stored or shared without being formally managed by the IT team. Often as a result of employees creating and storing files on unauthorized platforms and devices. You can't protect what you don't know exists.
A local insurer discovered that their claims adjusters had been storing customer ID copies, medical reports, and KYC data on personal Google Drive and WhatsApp groups for “easier access.” IT had no visibility. A disgruntled manager leaked the data, leading to a regulatory fine from the Office of the Data Protection Commissioner (ODPC).
What are the Remedies?
1. Keep an Accurate Asset Inventory.
It is important to know what you have. Finding all your systems and devices that can be reached from the internet is a crucial first step. This gives a comprehensive view of your digital footprint not to let any system unmonitored.
We conducted this on a mid-sized logistics company in Mombasa and found 14 forgotten servers, some still running outdated software connected to their network. One of them was a payment gateway test server still active in production.
2. Perform regular Security Assessments.
A routine health check is mandatory. It goes beyond vulnerability scans to evaluate whether your security controls and defense strategies are effective.
A Nairobi hospital assumed they were compliant because they ran quarterly vulnerability scans. A proper security assessment revealed that their radiology imaging system (connected to the internet) had default admin credentials. That single finding prevented a potential ransomware attack like those seen in Ireland and the US.
3. Develop Collaborative Security Processes
Cybersecurity is not the sole preserve of the IT or Security department. It requires collaboration across every department. That’s why training communication, sales and HR department on matters Security is as important as implementing an Endpoint detection System.
A large SACCO trained their front-office, marketing, and HR teams on spotting phishing and reporting unusual data requests. Within six months, the HR team flagged a fake CEO email asking for payroll records—stopping a social engineering attack before any loss.
What We Do at South-End Tech
At South-End Tech, we believe in pragmatic security. We don't chase buzzwords; we implement systems that provide real cybersecurity visibility, backed by the same best practices we’ve used to secure businesses across Kenya and beyond.
That means continuous asset inventory. Ongoing system monitoring. Frequent vulnerability testing. We don't just trust what we see on the surface we test what we've got.
This is a wake-up call for every organization. Do you really have visibility into your systems? Or are you next in line to find out the hard way?
Ready to assess your organization's Security Posture? Let us talk.
Telephone: +254 728223333 | +254 717335467
Email: tabuta@southendtech.co.ke | cybersecurity@southendtech.co.ke | info@southendtech.co.ke |
South-End Tech Limited — Helping businesses build visible and Cyber-resilient Enterprises.